Introduction
Network Traffic Analysis in 2025 has become a fundamental requirement for organizations managing complex enterprise systems. With the exponential growth of cloud computing, distributed architectures, and data-intensive applications, monitoring network behavior is no longer optional—it is critical.
Enterprises today handle massive volumes of data flowing across networks every second. This data includes user activity, API calls, system communications, and external traffic. Without proper analysis, detecting malicious activity or performance issues becomes nearly impossible.
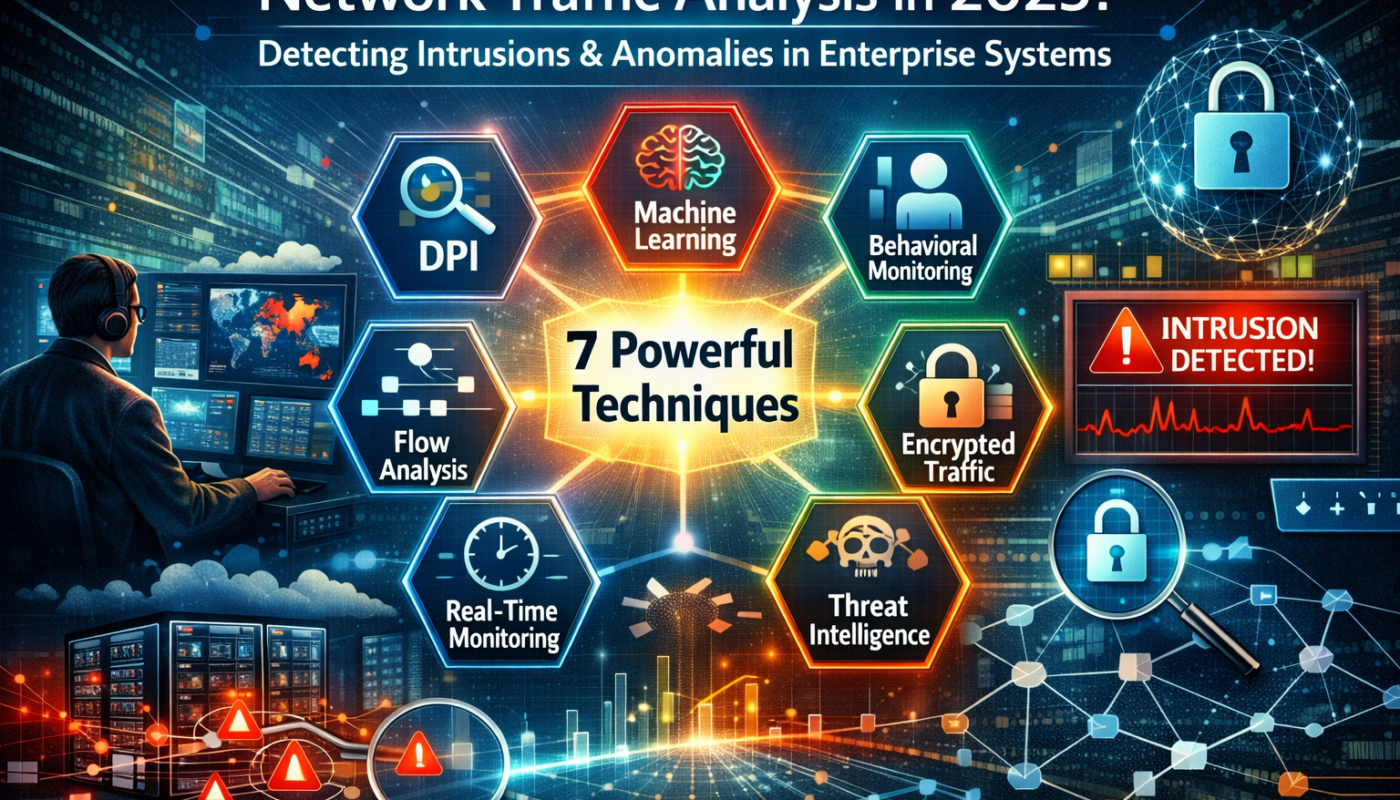
Network Traffic Analysis enables organizations to monitor, capture, and evaluate network data in real time to identify intrusions, anomalies, and inefficiencies. This blog explores 7 powerful network traffic analysis techniques that help businesses secure and optimize their enterprise systems.

What is Network Traffic Analysis?
Network Traffic Analysis is the process of capturing and inspecting data packets flowing across a network to understand behavior, detect threats, and improve performance.
Key Functions:
- Monitoring incoming and outgoing traffic
- Identifying suspicious patterns
- Detecting anomalies and intrusions
- Optimizing network performance
It provides deep visibility into system operations and helps security teams respond proactively.
Why Network Traffic Analysis is Critical in 2025
Modern enterprise systems are:
- Distributed across cloud environments
- Built on microservices architecture
- Highly dynamic and scalable
Without proper analysis, organizations face:
Risks:
- Data breaches
- Unauthorized access
- System downtime
- Performance bottlenecks
Benefits:
- Real-time threat detection
- Improved system reliability
- Faster troubleshooting
- Better resource utilization
7 Powerful Network Traffic Analysis Techniques
1. Deep Packet Inspection (DPI)
Deep Packet Inspection analyzes the actual content of data packets rather than just metadata.
Benefits:
- Detects hidden threats
- Identifies malicious payloads
- Provides detailed traffic visibility
Advanced Use:
DPI is used in enterprise firewalls and intrusion detection systems to identify sophisticated attacks.
2. Flow-Based Traffic Analysis
This technique focuses on analyzing traffic flow between systems rather than inspecting individual packets.
Benefits:
- Lightweight and scalable
- Suitable for large networks
- Helps identify traffic patterns
Example:
Tracking communication between services in microservices architecture.
3. Anomaly Detection Using Machine Learning
Machine learning models detect unusual behavior in network traffic.
Benefits:
- Identifies unknown threats
- Reduces false positives
- Adapts to changing patterns
Advanced Insight:
AI models continuously learn from data and improve detection accuracy.
4. Behavioral Traffic Analysis
This technique analyzes user and system behavior over time.
Benefits:
- Detects insider threats
- Identifies abnormal activities
- Enhances security monitoring
Example:
Detecting unusual login attempts or data access patterns.
5. Real-Time Traffic Monitoring
Real-time monitoring ensures continuous visibility into network activity.
Benefits:
- Immediate threat detection
- Faster incident response
- Reduced downtime
Tools:
Used in Security Operations Centers (SOC) for live monitoring.
6. Encrypted Traffic Analysis
With increasing use of encryption, analyzing encrypted traffic is essential.
Benefits:
- Detects threats without decryption
- Maintains privacy compliance
- Identifies suspicious encrypted patterns
7. Threat Intelligence Integration
Combining external threat intelligence with internal traffic data improves detection.
Benefits:
- Identifies known attack patterns
- Enhances detection accuracy
- Improves response time
Example:
Blocking malicious IP addresses using global threat databases.
Tools Used in Network Traffic Analysis
Organizations use various tools to implement these techniques:
- Wireshark (packet analysis)
- Nmap (network scanning)
- Zeek (network monitoring)
- Splunk (data analysis and logging)
These tools help capture, analyze, and visualize network traffic efficiently.
Challenges in Network Traffic Analysis
Despite its benefits, organizations face several challenges:
- Handling large data volumes
- Encrypted traffic visibility issues
- High infrastructure costs
- False positives in detection
Best Practices for Enterprise Systems
To maximize the effectiveness of network traffic analysis:
- Use layered monitoring approaches
- Implement AI-driven detection systems
- Continuously update threat intelligence
- Monitor traffic in real time
- Optimize network performance regularly
Future of Network Traffic Analysis
The future of network traffic analysis will be driven by automation and intelligence.
Key Trends:
- AI-powered anomaly detection
- Predictive traffic analysis
- Automated incident response
- Self-healing networks
Organizations will rely more on intelligent systems that can detect and respond to threats autonomously.
Conclusion
Network Traffic Analysis in 2025 is essential for detecting intrusions and anomalies in enterprise systems. As networks become more complex, traditional monitoring methods are no longer sufficient.
By implementing these 7 powerful network traffic analysis techniques, organizations can gain deep visibility into their systems, improve security, and optimize performance. The integration of AI, real-time monitoring, and threat intelligence will continue to shape the future of network security and enterprise infrastructure.